Investigation into DES cracking with John the Ripper and Ztex FPGA
DES has not been considered safe for a long time. For some time now, cracking tool John the Ripp has even made it possible to accelerate cracking with FPGAs. Since I find this topic exciting, I tried it with an FPGA board.
System
- Lenovo Thinkpad X230
- Ubuntu 18.04 LTS
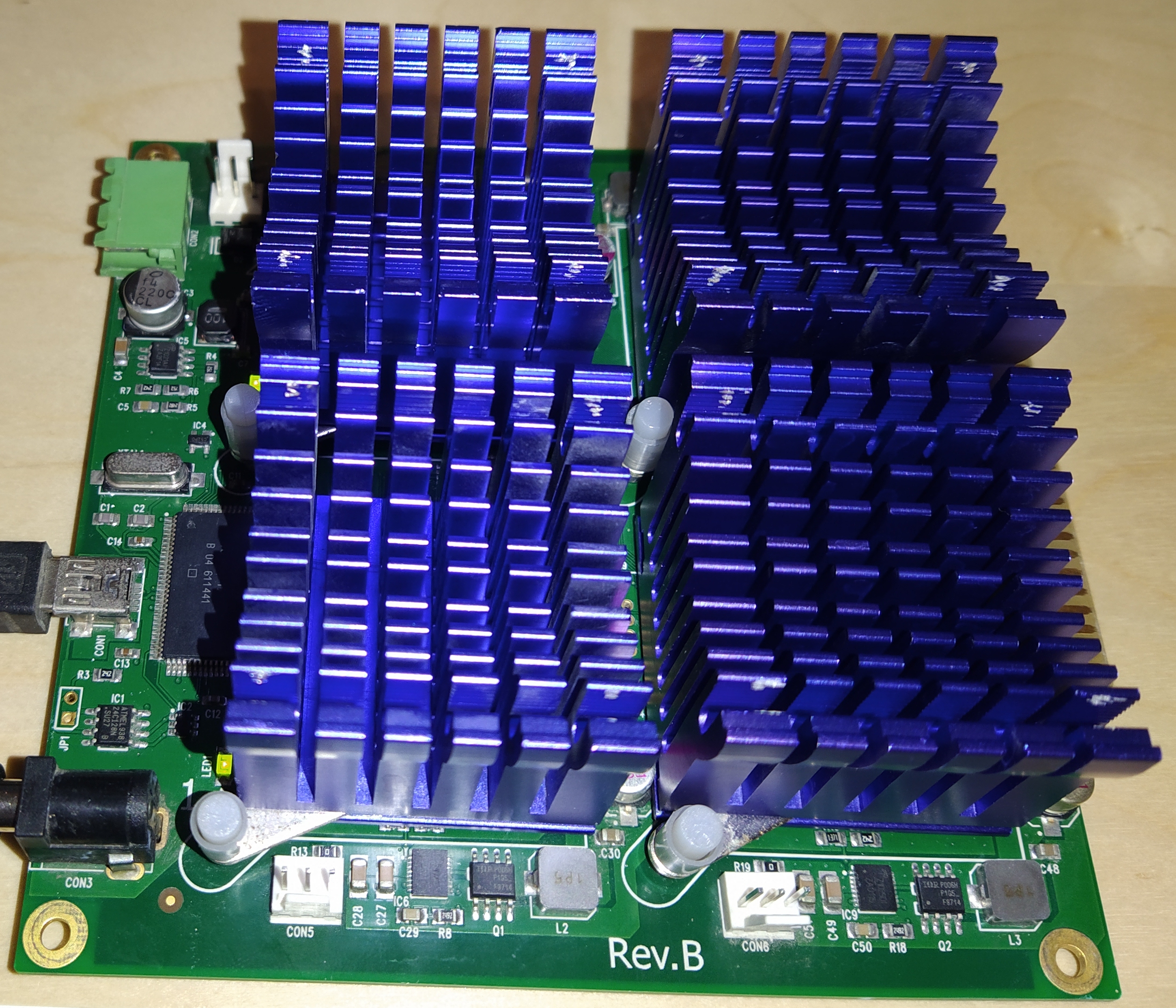
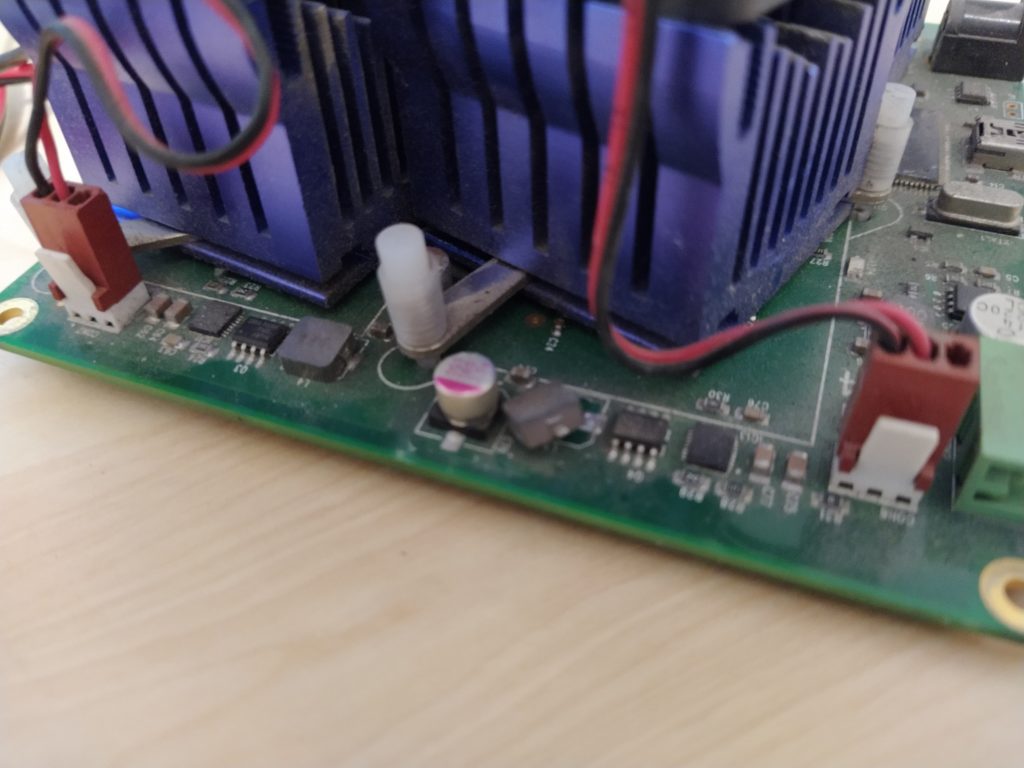
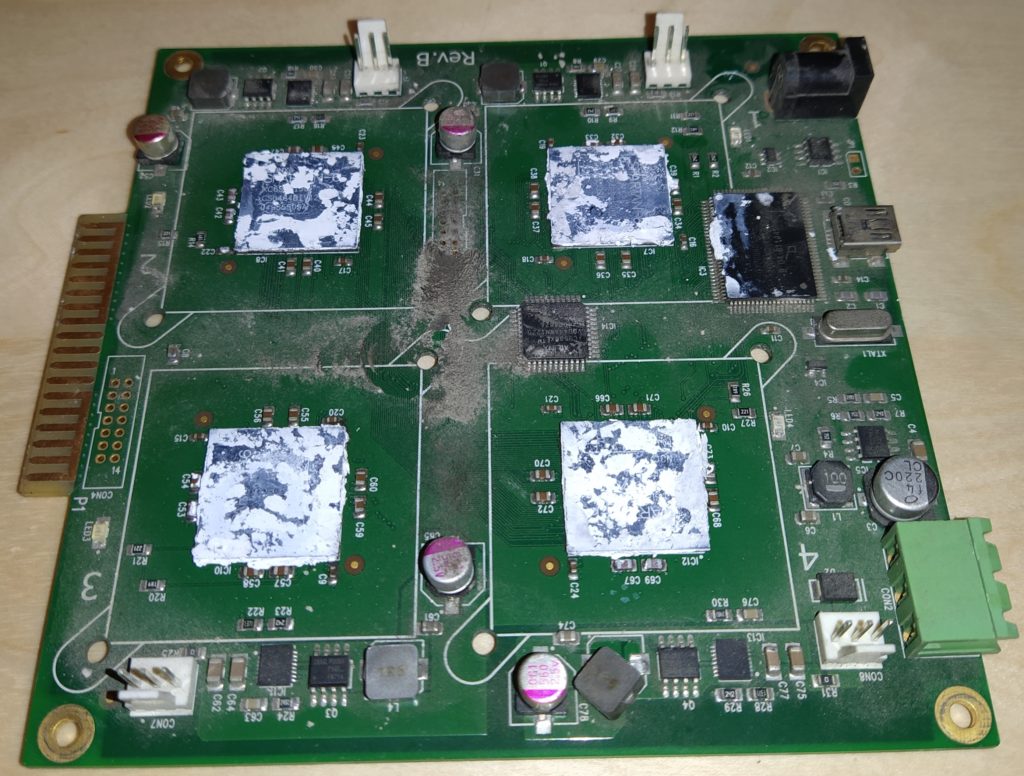
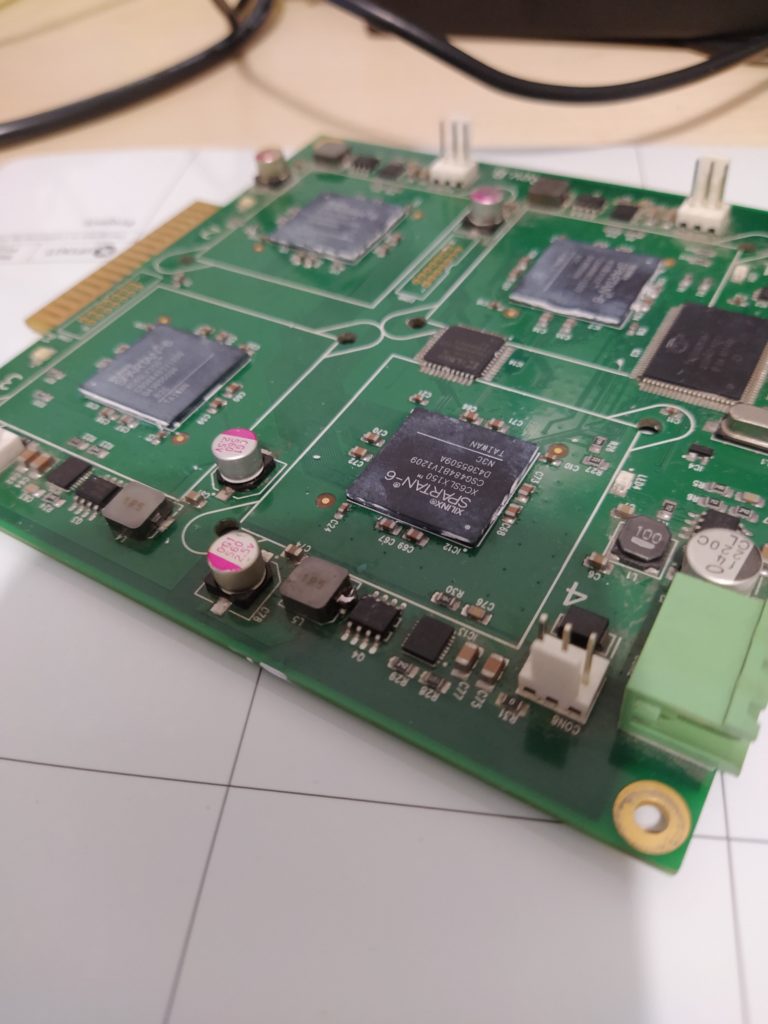
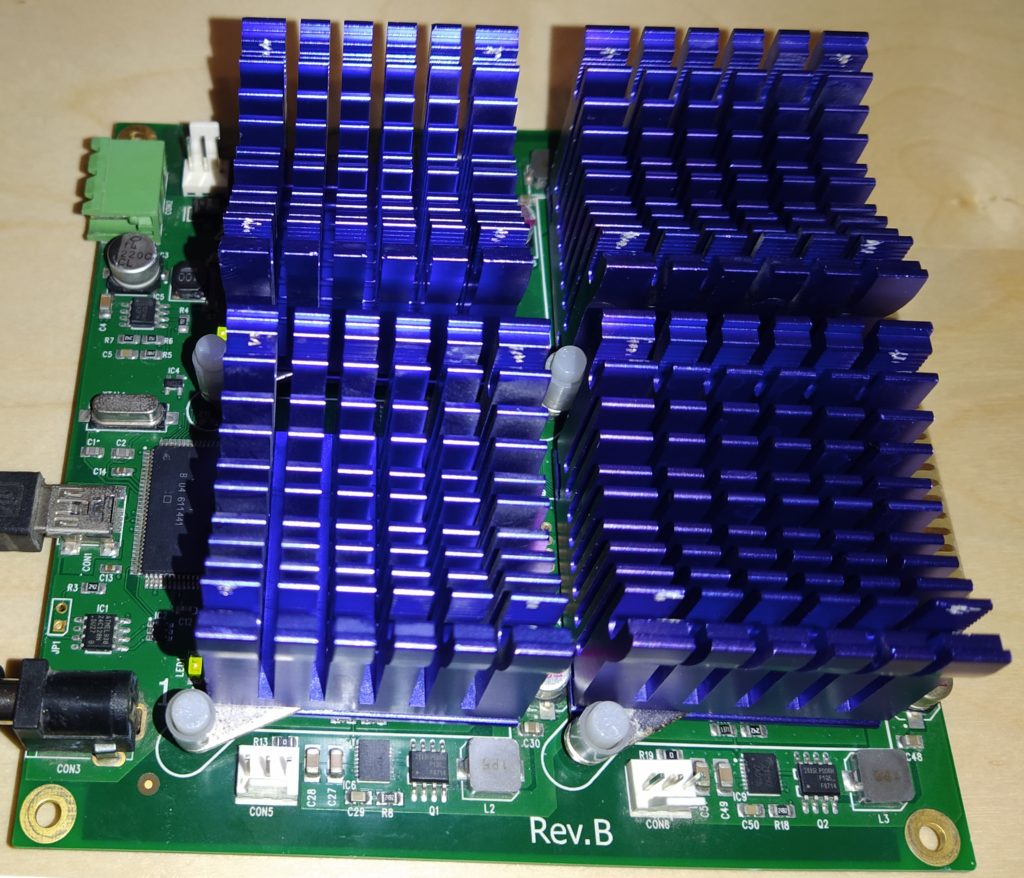
- Ztex 1.15y FPGA Board
Install necessary requirements:
sudo apt install libbz2-1.0 libbz2-dev libgmp-dev libkrb5-dev libnss3-dev libpcap0.8-dev libpcap-dev libssl-dev libusb-dev pkg-config python-usb yasm zlib1g-dev libusb-1.0 git
Clone John the Ripper
mkdir ~/gits
cd ~/gits
git clone https://github.com/magnumripper/JohnTheRipper.git
cd ~/gits/JohnTheRipper/src
./configure --enable-ztex
make -s clean && make -sj4
We generate a new example shadow file, to test the DES cracking
root:roEhj0vy.MdZw:16560:0:99999:7:::
daemon:*:16560:0:99999:7:::
bin:*:16560:0:99999:7:::
sys:*:16560:0:99999:7:::
sync:*:16560:0:99999:7:::
games:*:16560:0:99999:7:::
man:*:16560:0:99999:7:::
lp:*:16560:0:99999:7:::
mail:*:16560:0:99999:7:::
news:*:16560:0:99999:7:::
uucp:*:16560:0:99999:7:::
proxy:*:16560:0:99999:7:::
www-data:*:16560:0:99999:7:::
backup:*:16560:0:99999:7:::
list:*:16560:0:99999:7:::
irc:*:16560:0:99999:7:::
gnats:*:16560:0:99999:7:::
nobody:*:16560:0:99999:7:::
messagebus:!:16560:0:99999:7:::
And test the cracking with the following parameters
sudo ~/gits/JohnTheRipper/run/john -form=descrypt-ztex --progress-every=60 -inc=lower -min-len=8 -max-len=8 -mask='?w?l?l?l?l' shadow
The output should look like this
SN: XXXXXXXXXX productId: 10.15.0.0 "inouttraffic 1.0.0 JtR" busnum:1 devnum:6
Using default input encoding: UTF-8
Loaded 1 password hash (descrypt-ztex, traditional crypt(3) [DES ZTEX])
SN XXXXXXXXXX FPGA #2 error: pkt_comm_status=0x01, debug=0x0000
SN XXXXXXXXXX error -1 doing r/w of FPGAs (LIBUSB_ERROR_IO)
SN XXXXXXXXXX FPGA #2 error: pkt_comm_status=0x09, debug=0x0000
SN XXXXXXXXXX error -1 doing r/w of FPGAs (LIBUSB_ERROR_IO)
Press 'q' or Ctrl-C to abort, almost any other key for status
testtest (root)
1g 0:00:00:02 DONE (2020-02-10 14:10) 0.3875g/s 952210Kp/s 952210Kc/s 952210KC/s testtest..tonyaikz
Use the "--show" option to display all of the cracked passwords reliably
Session completed


Where did you get the board? I wanna make some experiments like yours but finding a compatible board has proven to be a very difficult task. I would really appreciate if you could give directions on how to get one.
I bought it on eBay… When i bought it there were quite a lot of these available… But currently I do not find any boards.
Would you consider selling or analyze a bcrypt hash?
No sorry, because I am not sure if this is legal in Germany.
I used one of eight boards to test, but the following error occurred.
sudo ./john -form=descrypt-ztex –progress-every=60 -inc=lower -min-len=8 -max-len=8 -mask=’?w?l?l?l?l’ shadow
SN: 04A39E2D6F productId: 10.15.0.0 “inouttraffic 1.0.0 JtR” busnum:1 devnum:9
Using default input encoding: UTF-8
Loaded 1 password hash (descrypt-ztex, traditional crypt(3) [DES ZTEX])
Press Ctrl-C to abort, or send SIGUSR1 to john process for status
SN 04A39E2D6F FPGA #2 error: app_status=0x10, debug=0x0000
SN 04A39E2D6F error -1 doing r/w of FPGAs (LIBUSB_ERROR_IO)
SN 04A39E2D6F FPGA #2 error: app_status=0x10, debug=0x0000
SN 04A39E2D6F error -1 doing r/w of FPGAs (LIBUSB_ERROR_IO)
SN 04A39E2D6F FPGA #3 error: app_status=0x10, debug=0x0000
SN 04A39E2D6F error -1 doing r/w of FPGAs (LIBUSB_ERROR_IO)
I also get the error message some times. I figured out, that it is important to connect the USB first and if the upload failed, power cycle the board.
sudo ~/gits/JohnTheRipper/run/john -form=descrypt-ztex –progress-every=60 -inc=lower -min-len=8 -max-len=8 -mask=’?w?l?l?l?l’ shadow
SN 04A36E36DC: firmware uploaded
SN: 04A36E36DC productId: 10.15.0.0 “inouttraffic 1.0.0 JtR” busnum:1 devnum:9
Using default input encoding: UTF-8
Loaded 1 password hash (descrypt-ztex, traditional crypt(3) [DES ZTEX])
SN 04A36E36DC: uploading bitstreams.. ok
SN 04A36E36DC: Timeout.
Press Ctrl-C to abort, or send SIGUSR1 to john process for status
SN 04A36E36DC FPGA #1 error: pkt_comm_status=0x01, debug=0x0000
SN 04A36E36DC error -1 doing r/w of FPGAs (LIBUSB_ERROR_IO)
testtest (root)
1g 0:00:00:16 DONE (2021-01-28 13:39) 0.06002g/s 147461Kp/s 147461Kc/s 147461KC/s testtest..tonyaikz
Use the “–show” option to display all of the cracked passwords reliably
Session completed.