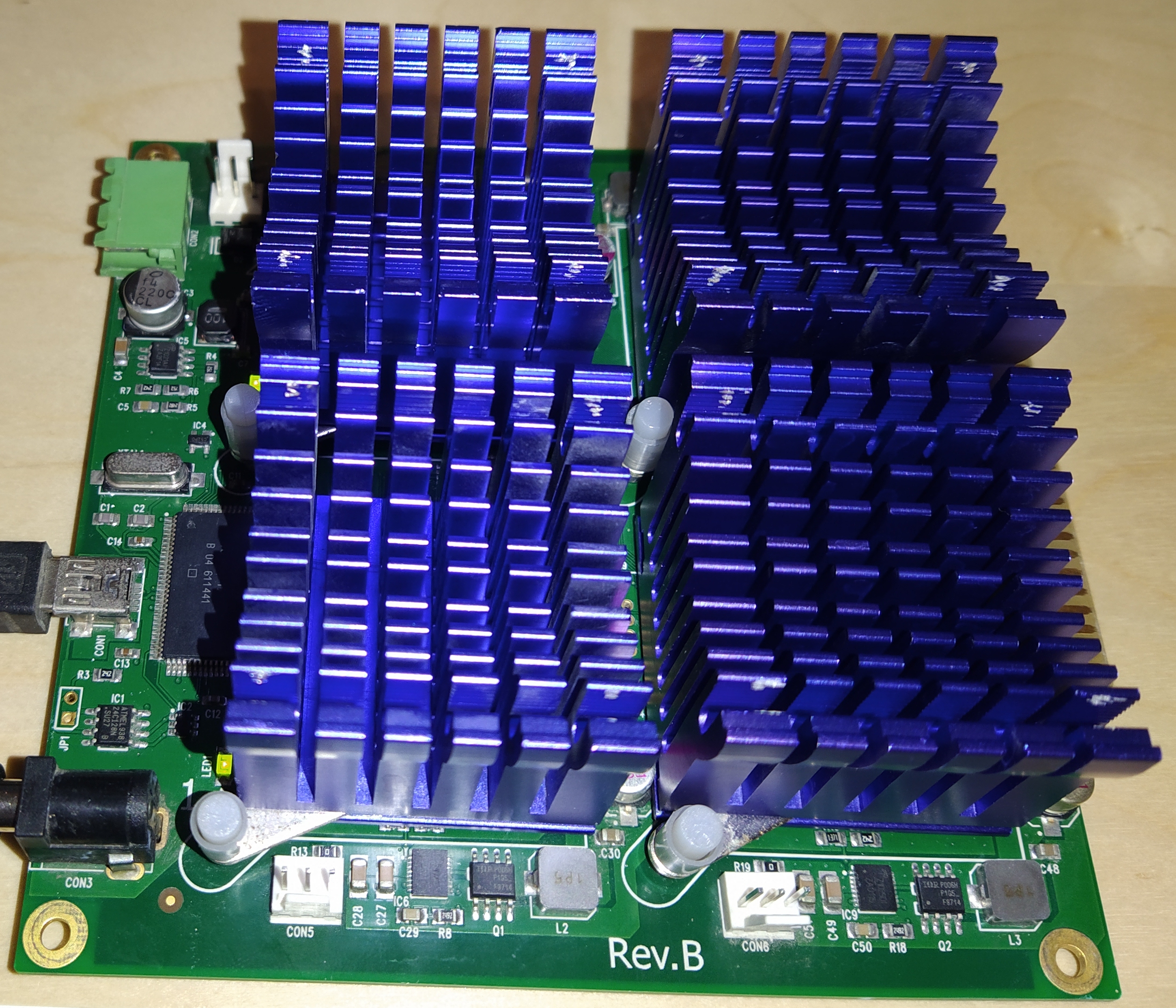
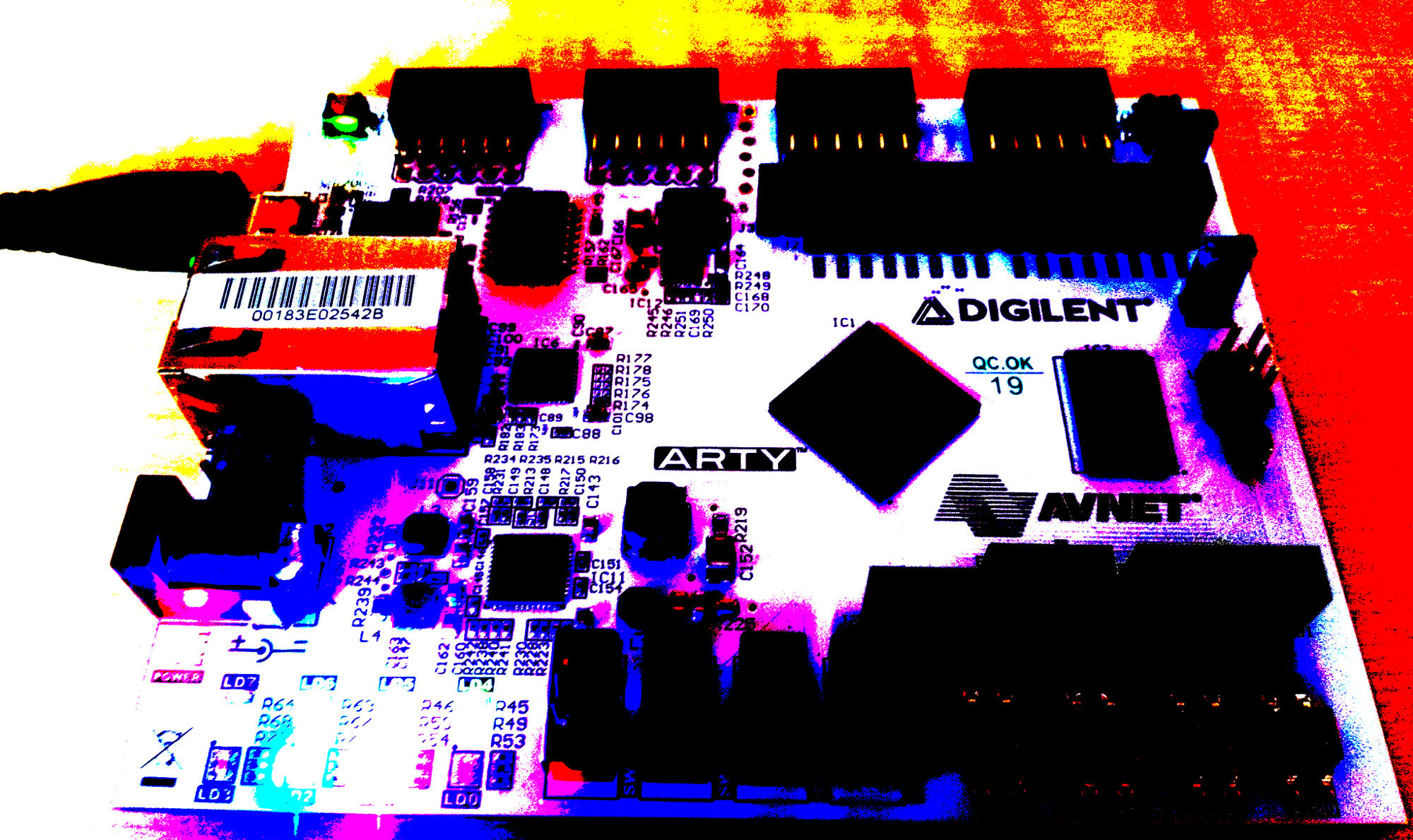
Investigation into DES cracking with John the Ripper and Ztex FPGA
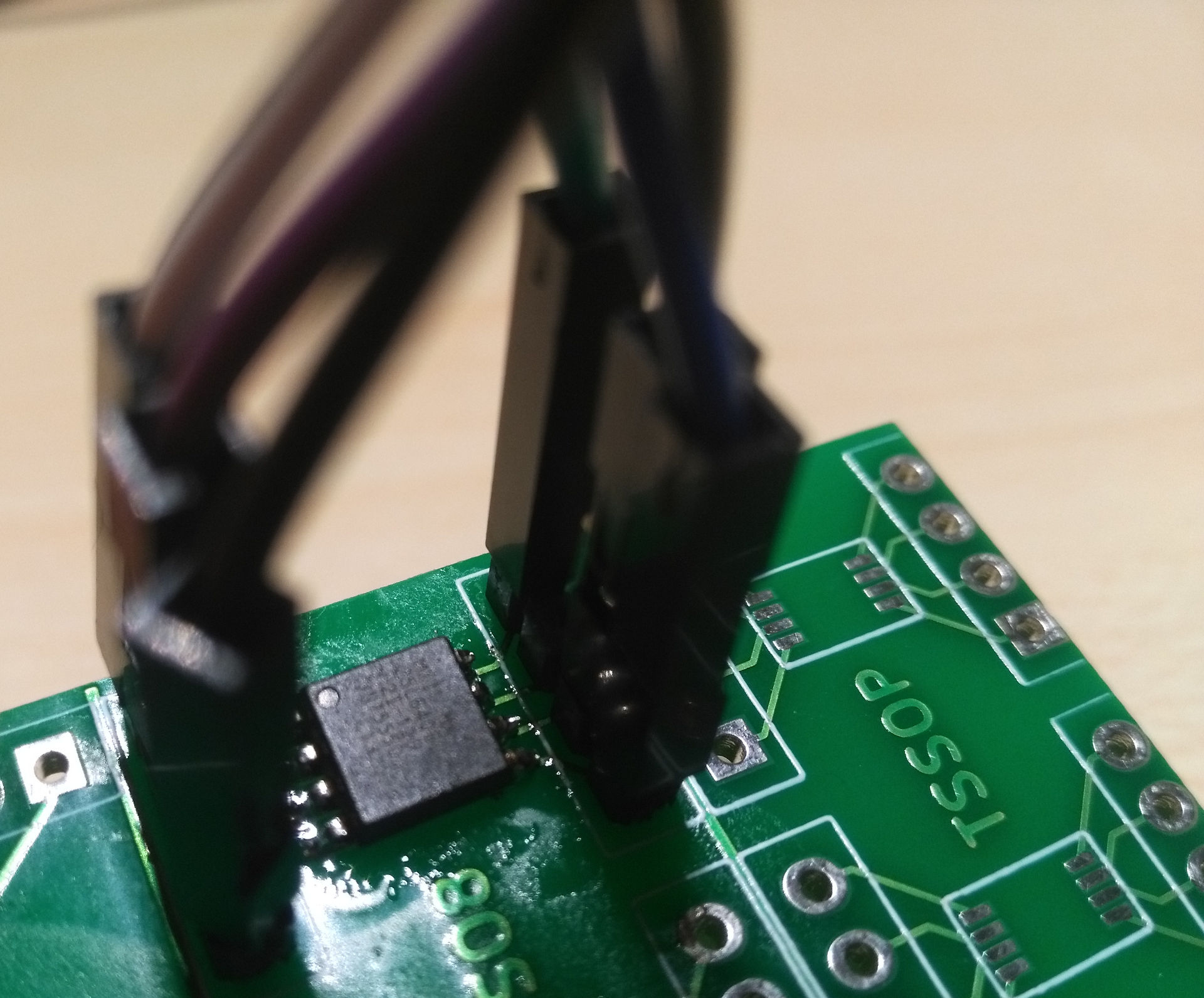
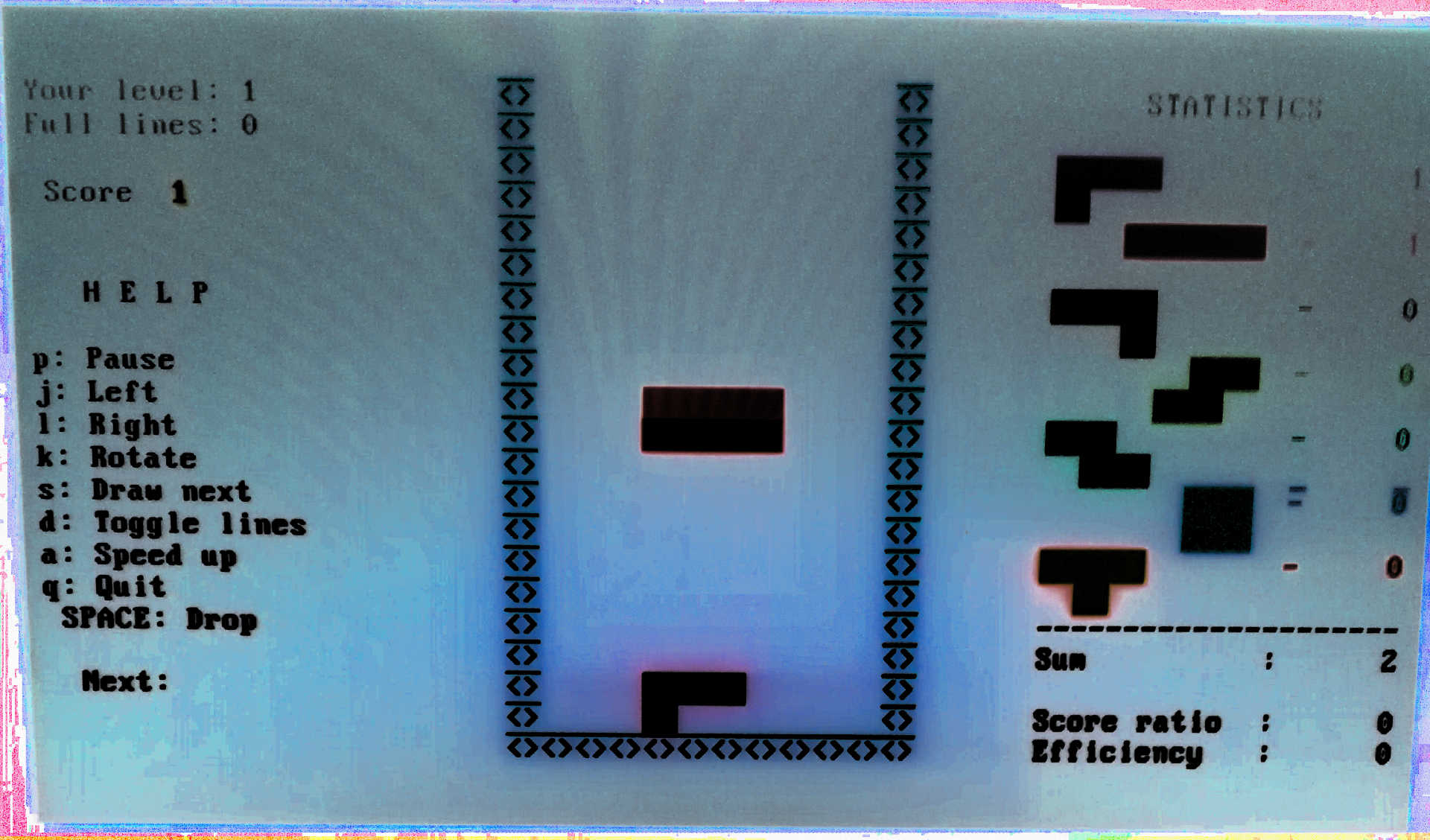
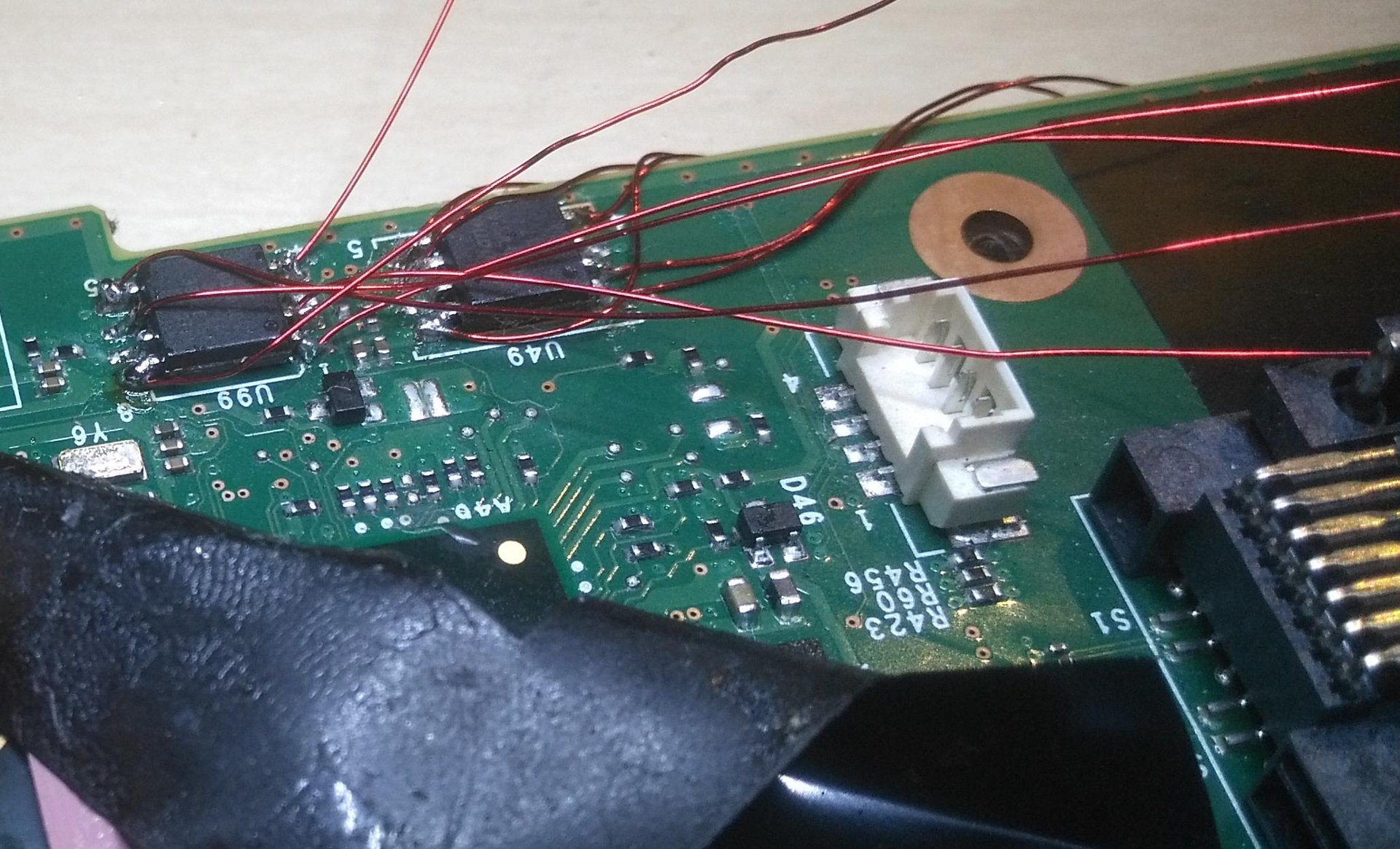
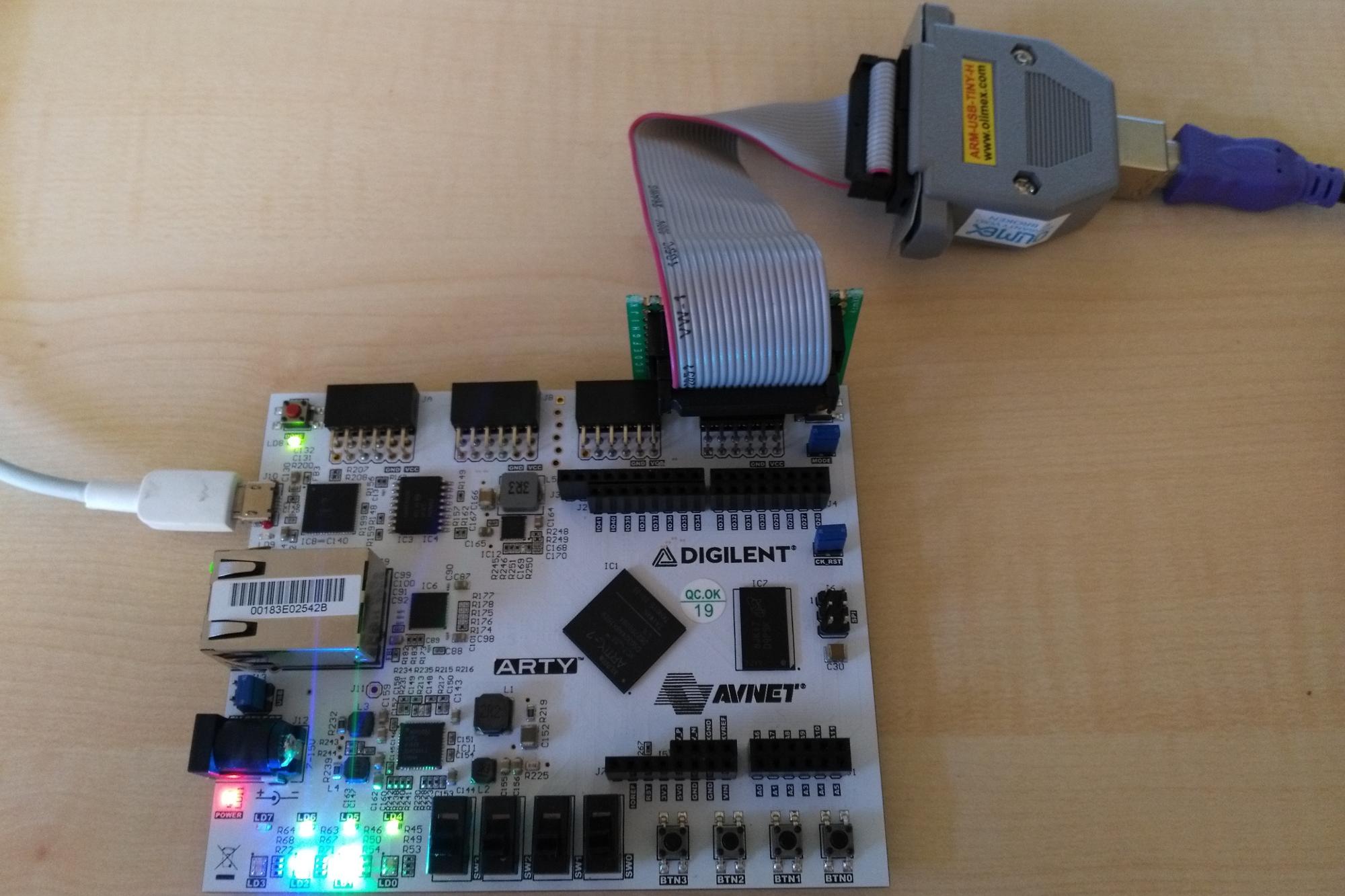
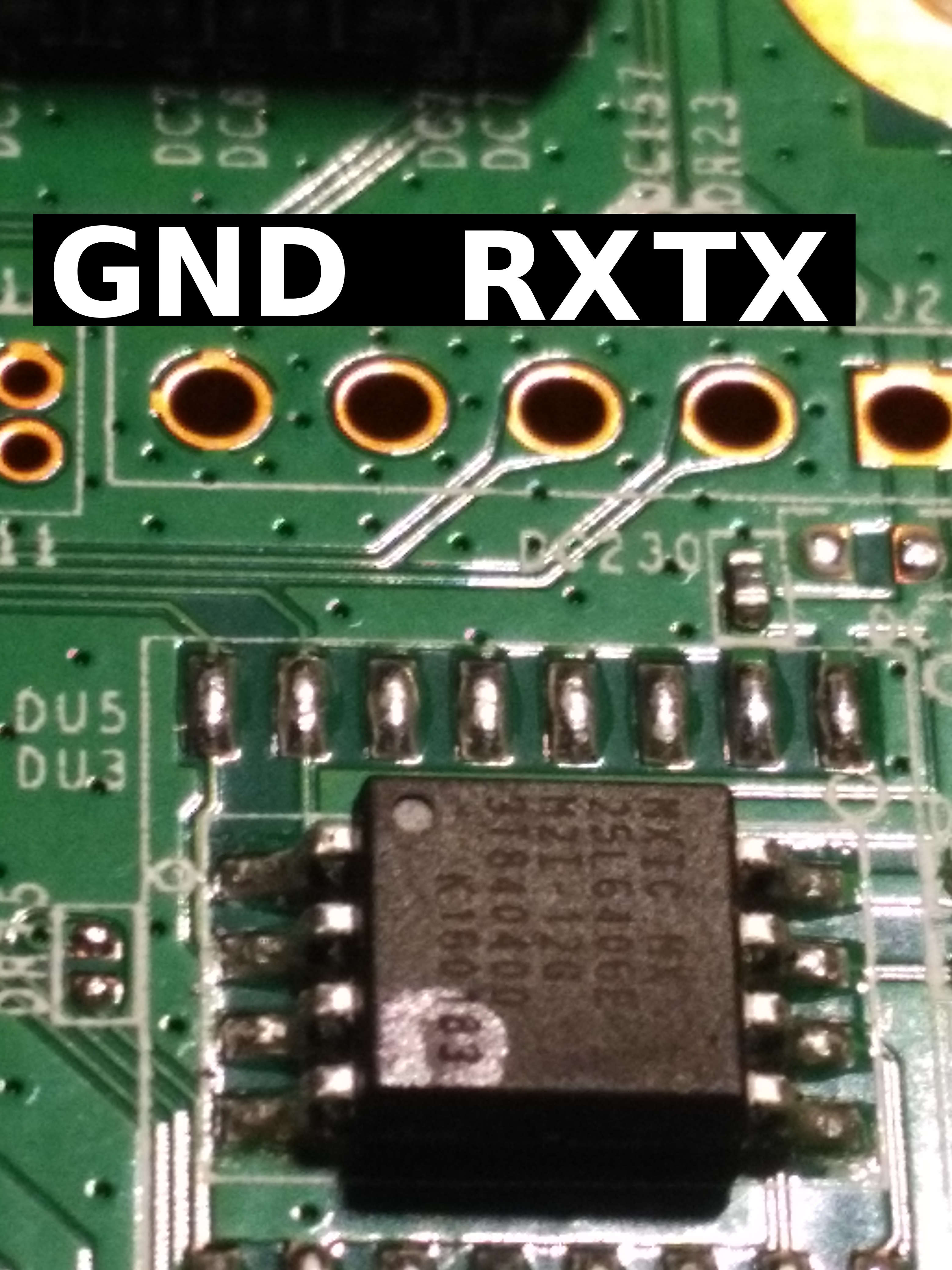
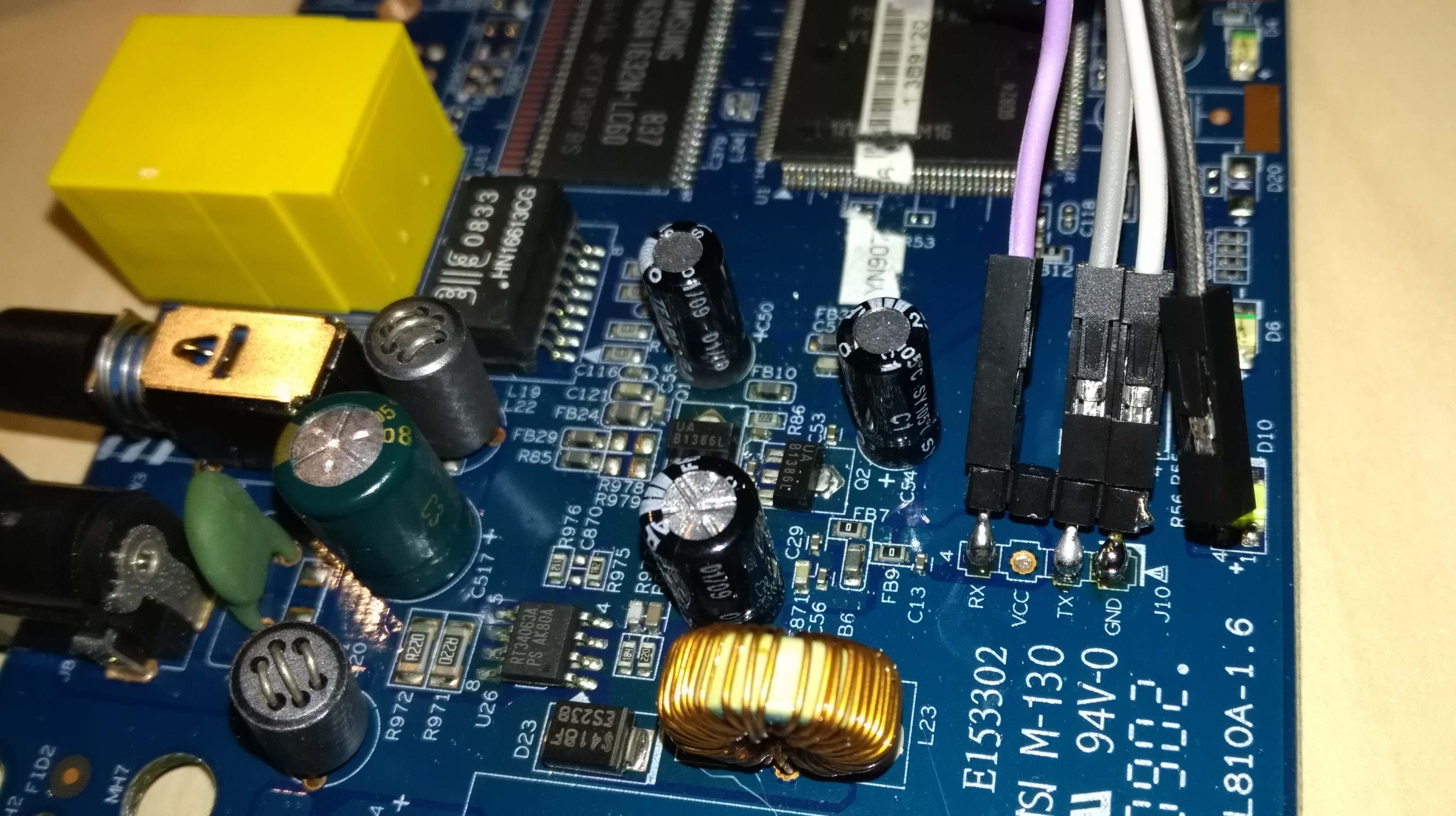
DES has not been considered safe for a long time. For some time now, cracking tool John the Ripp has even made it possible to accelerate cracking with FPGAs. Since I find this topic exciting, I tried it with an …
Investigation into DES cracking with John the Ripper and Ztex FPGA Read more »