Hacking – Root @ Linksys E900 N300
How to get root at Linksys E900 N300
The aim of this post is to get root access on the Linksys E900 N300.
To open the case the screws on the bottom of it must be removed. After that, the PCB could be detached from the case.
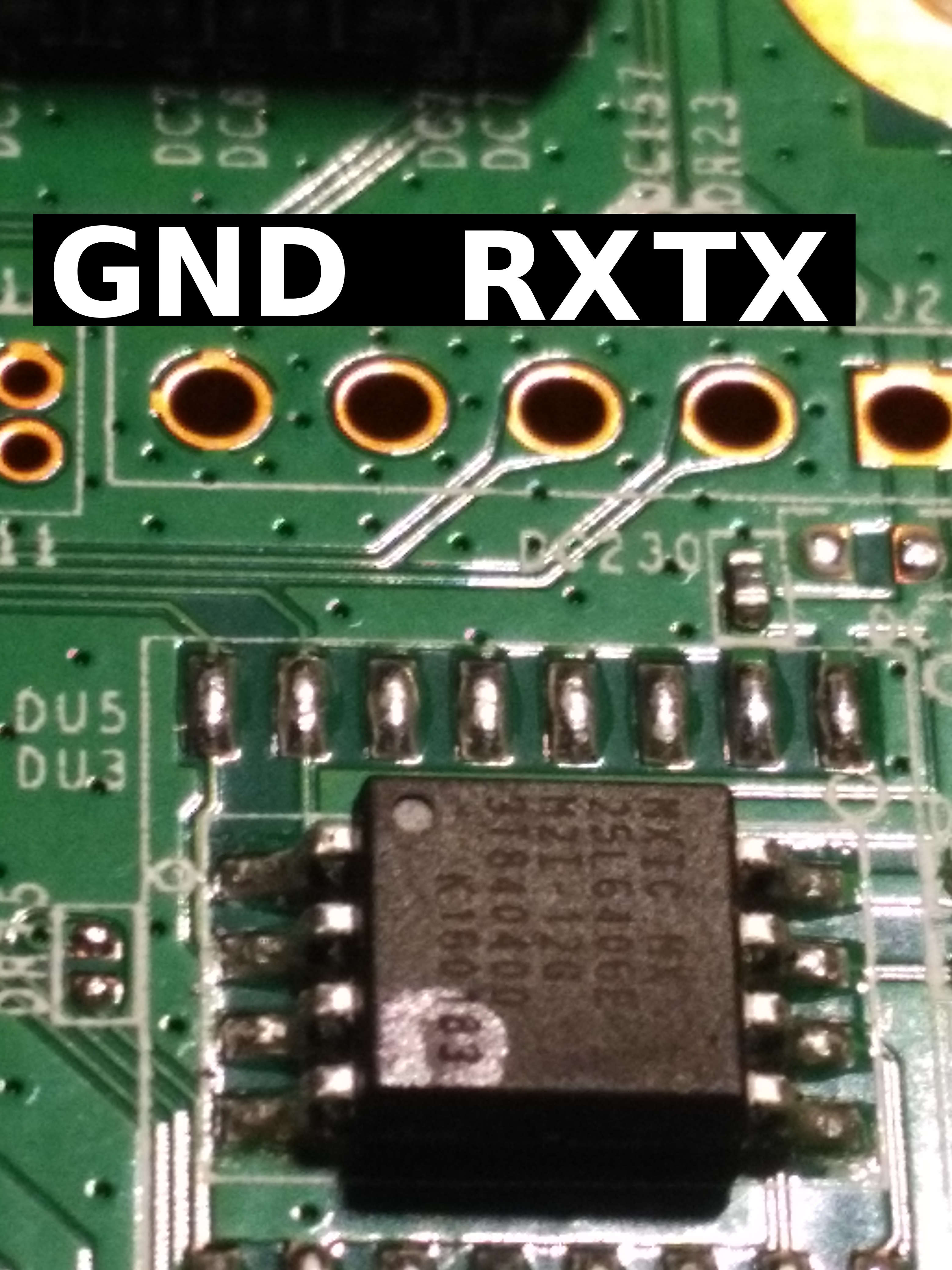
On the top right of the PCB there are five unequipped solder pads.
This indicates an UART.
To find out the pin layout a closer look at the routes is necessary. The left pin has a thermal relief (cross), which is often used for ground connections. The signal for RX and TX can be found out by brute force, the two pads with the small signal connections.
$ sudo picocom -b 115200 /dev/ttyUSB0 picocom v1.7 port is : /dev/ttyUSB0 flowcontrol : none baudrate is : 115200 parity is : none databits are : 8 escape is : C-a local echo is : no noinit is : no noreset is : no nolock is : no send_cmd is : sz -vv receive_cmd is : rz -vv imap is : omap is : emap is : crcrlf,delbs, Terminal ready Decompressing...done Start to blink diag led ... CFE version 5.100.138.11 based on BBP 1.0.37 for BCM947XX (32bit,SP,LE) Build Date: 01/08/15 11:53:36 CST (root@Richard-Linux) Copyright (C) 2000-2008 Broadcom Corporation. Initializing Arena Initializing Devices. No DPN This is a Serial Flash Boot partition size = 262144(0x40000) Found an ST compatible serial flash with 128 64KB blocks; total size 8MB Partition information: boot #00 00000000 -> 0003FFFF (262144) trx #01 00040000 -> 0004001B (28) os #02 0004001C -> 007EFFFF (8060900) nvram #03 007F0000 -> 007FFFFF (65536) Partition information: boot #00 00000000 -> 0003FFFF (262144) trx #01 00040000 -> 007EFFFF (8060928) nvram #02 007F0000 -> 007FFFFF (65536) BCM47XX_GMAC_ID et0: Broadcom BCM47XX 10/100/1000 Mbps Ethernet Controller 5.100.138.11 CPU type 0x19749: 300MHz Total memory: 32768 KBytes CFE mem: 0x80700000 - 0x807AE1F0 (713200) Data: 0x80743460 - 0x80747540 (16608) BSS: 0x80747540 - 0x807481F0 (3248) Heap: 0x807481F0 - 0x807AC1F0 (409600) Stack: 0x807AC1F0 - 0x807AE1F0 (8192) Text: 0x80700000 - 0x80743460 (275552) Boot version: v5.3.7 The boot is CFE mac_init(): Find mac [14:91:82:6d:f9:3d] in location 0 Nothing... [...] Hit enter to continue... BusyBox v1.7.2 (2015-01-08 11:49:52 CST) built-in shell (msh) Enter 'help' for a list of built-in commands. # cat /etc/passwd root::0:0:root:/:/bin/sh # echo "$USER" root
And we are done.





Leave a Reply